Authy vs. Google Authenticator
With every breach, every hack, every lost or stolen phone, online users have a similar thought: “I hope my private data didn’t just leak into the vast and very dark internet.”
There’s a good reason to fear: once your personal data is out there, it’s out there for good. That’s why online security is a trending topic these days. Usernames and passwords — no matter how clever they might be — aren’t protecting your accounts and devices anymore. And two-factor authentication, despite it being as simple to use as iTunes — is still far from being widely adopted.
In short, people are slow to change, and when people do change their minds about 2FA, they typically first come across Google Authenticator for protection, because Google permeates so much of the internet, anyway.
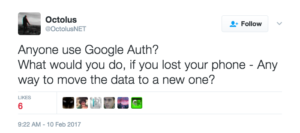
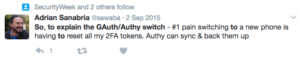
And it usually starts with a phone switch:
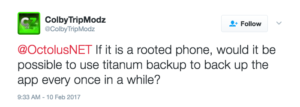
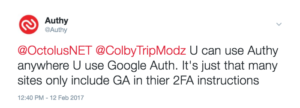
That’s when friends try to help:
Which often doesn’t help at all:
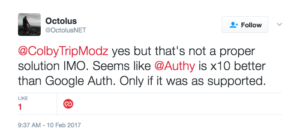
This requires a little clarification:

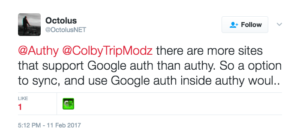
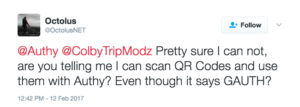
And the response:
Then the reveal:
Followed by resistance:
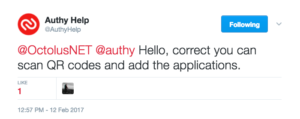
Our support team confirms:
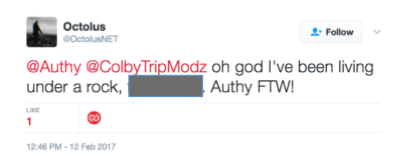
Resulting in this wonderful ‘a-ha’ moment:
It’s true. Google Authenticator, like Authy, generates a time-dependent six-digit code, which you enter after you submit your username and password. It’s not bad at providing necessary second-factor protection, for sure. And users are pretty satisfied, that is until a lost phone or a desire to switch devices forces them to make a change.
From our (obviously biased) perspective, there’s a lot to be desired when it comes to Google Authenticator. Let’s break it down:
Google Authenticator lacks multi-device support.
- With Authy’s multiple-device functionality, your 2FA tokens automatically sync to any new device you authorize. And, if a device is lost, stolen, or retired, you can deauthorize it from any authorized device just as quickly.
- Since Authy is available for Android, and iOS mobile devices, and for Windows, Apple Watch, and even your desktop, you can use Authy to stay protected from all devices simultaneously. Google Authenticator users are tied to a single device, so if you want to register a new phone or tablet, Google Authenticator automatically unregisters your current device.
- Some feel that having tokens on multiple devices is risky. So, if you fall into that camp, please note that Authy has made this feature optional and you can disable it at any time. Ready to link multiple devices? Start here.
Google Authenticator is only available on mobile devices.
- Some people are more mobile than others, but if you spend any time at all with a desktop computer, you’ll be happy to discover that Authy’s 2FA protection is also available as a browser extension. This proves especially convenient because desktops users — especially people who don’t have a smartphone or tablet — are no longer required to copy a security code delivered to their phone over to their laptop or desktop computer. Authy brings the entire 2FA security experience directly to the user regardless of device.
- While Google Authenticator is available for Android, BlackBerry, and iOS, there’s no desktop app. When connecting from a laptop or desktop to a service for which Google Authenticator is providing 2FA protection, you must have a mobile device on hand to generate your access codes.
Google Authenticator has no encrypted recovery backups.
- Out of the gate, Authy lets you take advantage of encrypted backups in the cloud. How is this handy? Lose a phone, and you can still access Authy accounts from other devices (as long as you have not disabled the multi-device feature). Get a new phone, and you can install the Authy app, verify your identity, and access all your Authy tokens relatively painlessly when compared to Google’s solution.
- Google Authenticator falls short when it comes to cloud sync options. With Google, if you lose your phone you lose your access. Get a new phone and prepare to manually transfer your accounts, all of them, one at a time. This scenario alone seems to be the biggest reason people switch from GA to Authy.
- And similarly to our multi-device feature, Authy’s cloud backups are entirely optional: there if you want it, but not mandatory. Read how our tokens are backed up and encrypted.
Google Authenticator has limited password protection.
- What makes Authy more secure than Google Authenticator is that our app keeps your tokens safe with three different types of passwords: Backup passwords, Master passwords, and PIN protection. Learn how each keeps your tokens secure.
Despite Google Authenticator’s recent make-over, our UI wins hands-down.
- Again, we’re biased, but Authy just looks better. And it has a great UI on all platforms and is easy to use on iPhone, Android, desktop, even Apple Watch. And there are three different authentication types available:
- OTP (One-Time Passcode) delivers SMS or Voice Call 2FA protection. While it’s not as strong as our other Authy authentication formats, it still provides better protection than a username and password alone. And it has the broadest global reach. We like to think of it as a best-option fall-back rather than remaining unprotected.
- Soft token TOTP (Time-based One-time Passwords) can generate 2FA codes even when your phone is not connected to a cell or data network, like when you’re on a plane or vacationing on some remote island.
- Push Authentication is the most secure, and most user-friendly way to deliver 2FA. It’s a push notification triggered solution for a streamlined user experience with advanced protection. Google Authenticator has no push notification capability.
Many who switch from Google Authenticator to Authy never look back.









So, now you’re armed and ready for the next time someone says both apps do pretty much the same thing.
They don’t. And now you know.
